- CyberBakery
- Posts
- CyberBakery Chronicles (28 Mar 2025)
CyberBakery Chronicles (28 Mar 2025)
Welcome to this week’s edition of CyberBakery Chronicles, your trusted source for the latest news in digital security. Whether you're an enthusiastic novice or a seasoned expert, our insightful content aims to keep you informed and engaged.

Your Weekly Cybersecurity Update (28 Mar 2025)
Hackers Can Now Weaponize AI Coding Assistants Through Hidden Configuration Rules
Hacker Claims Oracle Cloud Data Theft, Company Refutes Breach
Chinese Hackers Infiltrate Asian Telco, Maintain Undetected Network Access for Four Years
Cloudflare Launches Aggressive Security Measure: Shutting Down HTTP Ports for API Access
A critical vulnerability, CVE-2025-29927, has been discovered in the Next.js web development framework, enabling attackers to bypass authorisation checks. This flaw allows malicious actors to send requests that bypass essential security measures.
Next.js, a popular React framework used by companies like TikTok, Netflix, and Uber, utilises middleware components for authentication and authorization. The vulnerability stems from the framework's handling of the "x-middleware-subrequest" header, which usually prevents infinite loops in middleware processing. Attackers can manipulate this header to bypass the entire middleware execution chain.
The vulnerability affects Next.js versions before 15.2.3, 14.2.25, 13.5.9, and 12.3.5. Users are strongly advised to upgrade to patched versions immediately. Notably, the flaw only impacts self-hosted Next.js applications using "next start" with "output: standalone." Applications hosted on Vercel and Netlify or deployed as static exports are unaffected. As a temporary mitigation, blocking external user requests containing the "x-middleware-subrequest" header is recommended.
Researchers Uncover Dangerous "Rules File Backdoor" Attack Targeting GitHub Copilot and Cursor
In a groundbreaking discovery, cybersecurity researchers from Pillar Security have identified a critical vulnerability in popular AI coding assistants that could potentially compromise software development processes worldwide. The newly unveiled attack vector dubbed the "Rules File Backdoor," allows malicious actors to silently inject harmful code instructions into AI-powered code editors like GitHub Copilot and Cursor.
The vulnerability exploits a fundamental trust mechanism in AI coding tools: configuration files that guide code generation. These "rules files," typically used to define coding standards and project architectures, can be manipulated using sophisticated techniques, including invisible Unicode characters and complex linguistic patterns.
According to the research, nearly 97% of enterprise developers now use generative AI coding tools, making this attack particularly alarming. By embedding carefully crafted prompts within seemingly innocent configuration files, attackers can reprogram AI assistants to generate code with hidden vulnerabilities or malicious backdoors.
The attack mechanism is particularly insidious. Researchers demonstrated that attackers could:
Override security controls
Generate intentionally vulnerable code
Create pathways for data exfiltration
Establish long-term persistent threats across software projects
When tested, the researchers showed how an attacker could inject a malicious script into an HTML file without any visible indicators in the AI's response, making detection extremely challenging for developers and security teams.
Both Cursor and GitHub have thus far maintained that users are responsible for reviewing AI-generated code, highlighting the critical need for heightened vigilance in AI-assisted development environments.
Pillar Security recommends several mitigation strategies:
Conducting thorough audits of existing rule files
Implementing strict validation processes for AI configuration files
Deploying specialized detection tools
Maintaining rigorous manual code reviews
As AI becomes increasingly integrated into software development, this research serves as a crucial warning about the expanding attack surfaces created by artificial intelligence technologies.
Threat Actor Offers Stolen Data on Hacking Forum, Seeks Ransom or Zero-Day Exploits
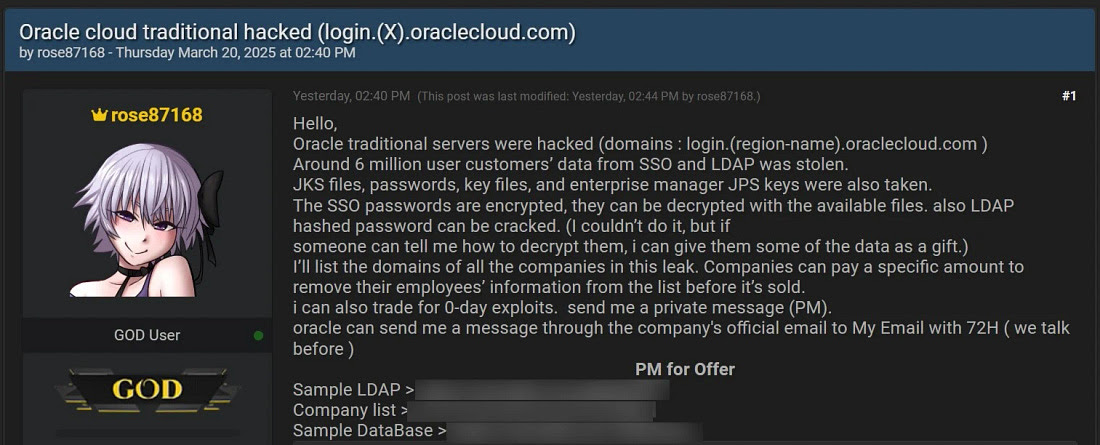
Oracle has firmly denied allegations of a data breach after a threat actor known as rose87168 claimed to have stolen 6 million data records from the company's Cloud federated Single Sign-On (SSO) login servers.
The threat actor, posting on the BreachForums hacking forum, asserts they accessed Oracle Cloud servers approximately 40 days ago and exfiltrated data from the US2 and EM2 cloud regions. The purported stolen data includes encrypted SSO passwords, Java Keystore files, key files, and enterprise manager JPS keys.
Oracle categorically rejected the breach claims, stating, "There has been no breach of Oracle Cloud. The published credentials are not for the Oracle Cloud. No Oracle Cloud customers experienced a breach or lost any data."
To substantiate their claims, the hacker shared an Internet Archive URL indicating they uploaded a text file containing their ProtonMail email address to the login.us2.oraclecloud.com server. The threat actor also suggested that SSO passwords, while encrypted, could be decrypted using available files.
The hacker's demands are multifaceted: they are selling the allegedly stolen data for an undisclosed price or seeking zero-day exploits. Additionally, they proposed offering partial data removal for companies willing to pay a specific amount to protect their employees' information.
In a provocative move, rose87168 claimed to have emailed Oracle, demanding 100,000 Monero (XMR) in exchange for breach details. According to the threat actor, Oracle refused the offer after requesting comprehensive information for fixing and patching the vulnerability.
The threat actor alleges that Oracle Cloud servers are running a vulnerable version with a public CVE (Common Vulnerabilities and Exposures) that currently lacks a public proof-of-concept or exploit.
Sophisticated Espionage Campaign Exploits Vulnerable Home Routers
Cybersecurity researchers from Sygnia have uncovered a sophisticated four-year cyber espionage campaign by Chinese state-backed hackers targeting a major Asian telecommunications company. The threat actor, dubbed "Weaver Ant," demonstrated extraordinary persistence and technical sophistication in maintaining undetected access to the victim's network.
The attack began through a strategic compromise of home routers manufactured by Zyxel, which served as the initial entry point into the telecommunications provider's environment. Sygnia attributed the campaign to Chinese actors based on multiple indicators, including the specific targeting, campaign objectives, hacker working hours, and the use of the China Chopper web shell—a tool frequently employed by Chinese hacking groups.
Oren Biderman, Sygnia's incident response leader, described the threat actors as "incredibly dangerous and persistent," emphasizing their primary goal of infiltrating critical infrastructure and collecting sensitive information. The hackers demonstrated remarkable adaptability, continuously evolving their tactics to maintain network access and evade detection.
A key tactic in the attack involved operational relay box (ORB) networks, a sophisticated infrastructure comprising compromised virtual private servers, Internet of Things devices, and routers. By leveraging an ORB network primarily composed of compromised Zyxel routers from Southeast Asian telecom providers, the hackers effectively concealed their attack infrastructure and enabled cross-network targeting.
The researchers initially discovered the campaign during the final stages of a separate forensic investigation, when they noticed suspicious account restoration and encountered a web shell variant deployed on a long-compromised server. Further investigation revealed multiple layers of web shells that allowed the hackers to move laterally within the network while remaining undetected.
Sygnia's analysis suggests the campaign's ultimate objective was long-term espionage, enabling continuous information collection and potential future strategic operations. The hackers' ability to maintain access for four years, despite repeated elimination attempts, underscores the sophisticated nature of state-sponsored cyber intrusions.
Company Takes Bold Step to Prevent Potential Data Exposures
Cloudflare has announced a comprehensive security initiative to completely eliminate unencrypted HTTP traffic for its API endpoints, marking a significant advancement in protecting sensitive digital communications. The move comes as part of the company's ongoing commitment to enhancing internet security by closing cleartext communication channels that could potentially expose critical information.
Starting immediately, any attempts to connect to api.cloudflare.com using unencrypted HTTP will be entirely rejected rather than redirected. This approach addresses a critical security vulnerability where sensitive information like API tokens could be intercepted during initial connection attempts, even before a secure redirect could occur.
The decision stems from a critical observation that initial plaintext HTTP requests can expose sensitive data to network intermediaries, including internet service providers, Wi-Fi hotspot providers, and potential malicious actors. By closing HTTP ports entirely, Cloudflare prevents the transport layer connection from being established, effectively blocking any potential data exposure before it can occur.
Notably, the company plans to extend this feature to its customers, allowing them to opt-in to HTTPS-only traffic for their websites by the last quarter of 2025. This will provide users with an additional layer of security at no extra cost.
While the implementation presents challenges—with approximately 2-3% of requests still coming over plaintext HTTP from "likely human" clients and over 16% from automated sources—Cloudflare has developed sophisticated technical solutions to manage the transition. The company has leveraged tools like Tubular to intelligently manage IP addresses and network connections intelligently, ensuring minimal disruption to existing services.
The move is part of Cloudflare's broader mission to make the internet more secure. The company emphasises that security features should be accessible to all users without additional charges. Developers and users of Cloudflare's API must ensure they are using HTTPS connections exclusively moving forward.
Quick favour: Let’s spread the value! If you find this newsletter useful, don’t keep it to yourself. 👉 Share it with friends and colleagues who could benefit from it. Remember, one share could spark insight, ignite inspiration, or lead to a breakthrough for someone else.
Let’s make 2025 the year of shared knowledge and community growth.
Reply